Related courses
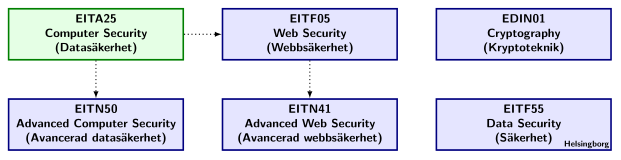
This course, EITA25 Computer Security is the first security course offered by EIT. It is is very broad and covers many different security related topics. It gives general security knowledge which is important for all engineers that work with computer systems, software or communication engineering. It also gives the foundation for the other security courses offered by the department.
The most natural next course in security is EITF05 Web Security. It is a 4.0hp G2-level course in HT1. Thus, Web Security is also a basic course but uses the cryptographic tools covered in this computer security course such as digital signatures, hash functions, symmetric and asymmetric encryption, and digital certificates. Web security covers several topics that are related to web technology. Some examples are
- Security principles for the web, e.g., the same origin policy and CORS.
- Web applications security, e.g., cross site scripting, cross site request forgery, SQL injections, remote and local file inclusion and session protection.
- Web server security, e.g., server configuration and common vulnerabilities related to this.
- Email security, e.g., spam prevention and detection, DKIM, SPF, DMARC and forged emails.
- DNS security, e.g., DNS architecture, amplification attacks, DNS cache poisoning, DNS rebinding and DNSSEC
Several of the most common attacks on the web are covered and the course also puts much focus on discussing available and potential defenses. After the course, you will be able to make web applications that are more secure than many of the popular web applications on the web. The topics covered in Web security are important for anyone working with technologies related to the internet and the web.
The course EITN50 Advanced Computer Security can be seen as a natural continuation of this course. It is a 7.5hp advanced level course in HT1. In that course, you will learn some selected computer security topics in more depth. These topics are
- Platform security, e.g., secure execution, trusted Computing, ARM Trustzone and virtualization.
- Software security, e.g., common security faults in programs, secure SW development processes, code analysis tools and Malware.
- Computer forensics.
- Digital Rights Management (DRM), e.g., copy protection of digital content.
- Network security.
The Advanced computer security course will cover topics in much more depth than this course and you will become well prepared for working with security. Several attacks and countermesures are discussed and there will also be projects that will give you practical experience with several important and interesting topics.
EITN41 Advanced Web Security builds on EITA25 Computer Security and EITF05 Web Security. It is a 7.5hp advanced level course in HT2. It uses the cryptographic basics, such as symmetric and asymmetric cryptography, included in EITA25 as well as Diffie-Hellman key agreement. The course also includes several new cryptographic topics, such as commitment schemes, zero-knowledge proofs and homomorphic encryption. These topics are introduced as a means to solve specific problems, such as e-voting and digital payment solutions. Thus, the treatment of the cryptographic aspects is very closely connected to a specific application. Examples of topics in he course is
- Electronic payments, e.g., 3D secure, card payments, e-cash, micropayments and Bitcoin.
- Anonymity, e.g., Chaum mixes, onion routing and attacks on anonymity.
- E-voting, e.g., mix-based voting protocols and homomorphic encryption based protocols.
- Data representation and PKIs, e.g., ASN.1, BER and DER encoding and PKCS-standards for representing cryptographic data.
- OpenID and OAuth.
After the Advanced web security course, you are well prepared to design and analyze new and advanced internet based protocols that require security. You will also be able to, in an informed way, participate in discussions on how to best design security from an industry perspective, knowing many of the state-of-the-art technologies, algorithms and tools.
In the security courses above, cryptographic algorithms are primarily given as a tool for realizing specific protocols. EDIN01 Cryptography provides a much deeper understanding of these tools. It is a 7.5hp advanced level course in HT2. In that course you will learn how to design and analyze many types of cryptographic algorithms. Examples of topics in that course is
- Classical cryptography, e.g., Caesar ciphers, substitution ciphers and rotor machines such as Enigma
- Stream ciphers and their building blocks, e.g., shift registers and nonlinear combiners.
- Block ciphers, e.g., DES and AES.
- Public key cryptography, e.g., basic number theory, RSA, factoring, primality and digital signatures.
- Hash functions, e.g., properties and collision attacks.
- Authentication codes, e.g., impersonation and substitution attacks.
- Secret sharing, e.g., Shamir’s threshold scheme, general secret sharing, perfect and ideal schemes.
After the cryptography course you will be able to make decisions concerning specific cryptographic primitives and determine which algorithms are suitable in a given environment.
The department also offers EITF55 Data Security which is an introductory course given in Helsingborg. It is similar to this computer security course and several of the same topics are covered.